1/52
@hackerfantastic
North Korea stole $1.4billion by injecting JavaScript through an AWS S3 bucket to spoof the UI interface during a transaction? It's almost like the entire infosec industry is focusing on hyperbolic amplified APT threats that are "cool" rather the stark realities confronting us.
2/52
@hackerfantastic
Note how few infosec and hacker types (exceptions exist) even talk about blockchain, web3 or crypto(the currency, not your lousy private keys) exploitation despite there being 1.4billion reasons why its currently trending amongst the world of clandestine nuclear finance programs.
3/52
@hackerfantastic
Imagine loosing *billions* because of javascript injection via cloud storage compromise though... ingenuis to simply spoof the UI interface whilst signing the transaction, gives some StuxNet vibes from HMI spoofing the values - proof that humans are still the weakest link.
4/52
@hackerfantastic
The backdoor, it defines a "whitelist" (wa) and "blacklist" (ba), if the transaction matched the whitelist, it redirected the transfer to smart contract "ta" (transfer) 0x9622[...] using data stored in "da", sending to smart contract 0xbdd077f651ebe7f7b3ce16fe5f2b025be2969516.
5/52
@hackerfantastic
This JS backdoor essentially allowed DPRK to drain the ByBit wallet using smart contracts when the caller was 0x0fa09C3A328792253f8dee7116848723b72a6d2e, effectively draining the wallets from the "whitelist", all other transactions were ignored. The attacker just wanted ByBit.
6/52
@hackerfantastic
The backdoor code is still available on the Wayback machine here
https://web.archive.org/web/2025021.../static/chunks/pages/_app-52c9031bfa03da47.js - it literally just hijacked a NeXT.js front-end when a transaction was being made from specific ByBit wallets, sending to smart contracts that could be drained by
Ethereum Transactions Information | Etherscan
7/52
@daKriptologist
"UI interface" is redundant, sir
because the I in IU is "interface"
I thought it was Inter-galactic, but Grok confirmed otherwise
8/52
@hackerfantastic
UI/UX, GUI, whatever, it's not that big of a deal but thank you for pointing it out. ;)
9/52
@chillippo
Do you have any more information on the code or domain they used?
I really would like to understand what happened
10/52
@hackerfantastic
cyber happened, leaky/stolen keys, write permissions to a bucket, well constructed backdoor in JS, pushed down to target specific users. There is a forensics report circling around, posted somewhere on the thread.
11/52
@duborges
javascript can make moneys
12/52
@hackerfantastic
Who knew that JS software engineers were worth a billion dollars?

13/52
@uwu_underground
This exact level of vulnerability exists in that space more often than people are willing to admit

14/52
@hackerfantastic
I am still mass-scanning for admin/123456. I'm a classic, like Mirai.
15/52
@Aleks13053799
People are the weak link. This is the key. Almost all crypto hacks from this group, and in general, have signs of social engineering/phishing.
16/52
@hackerfantastic
You can't patch away human behavior. ;) people click links, open websites and frequently follow direction - especially when the situation is conveying a sense of urgency or the emotional state is manipulated. This stuff works consistently.
17/52
@skrappy0x4a
Taking a non traditional infoSec job seems like a huge risk and I avoid it. Maybe others too.
18/52
@hackerfantastic
Taking risks is how you succeed in life. Nobody got rich by accepting a salaried SOC analyst position. They just get comfortable.
19/52
@0xdasha
isn’t APT threats a tautology
20/52
@hackerfantastic
I think we use the terms advanced too loosely to describe any tradecraft that isn't just running a tool like sqlmap.
21/52
@L1zrdk1ng
relying on javascript repositories to process transactions? you will never ever ever escape this exploit.
if banks get into crypto then they'll have to get into cli, and running nodes for every crypto they interact with.
22/52
@hackerfantastic
Yes, there is a need to improve many tools within the eco-system particularly across nodes and for the CLI for better integrations with the various technology stacks. The Layer3 and javascript part of this world is going to be an achilles heel for a time.
23/52
@windsheep_
Isn’t that something Content Security Policies can mitigate? Standard for any eCommerce. Difficult to do for Single Page Web Apps, but doable
24/52
@hackerfantastic
Could it have been stopped? Yes. Was it stopped? No. Little side hustle from the hackers unreleased handbook of awesome, CSP only applies to data you send, not data you fetch ;-)
25/52
@cyberseb_
Like the saying hackers don't care about security policies or MITRE.
26/52
@xpaulso
This reminded me of all the CPU cache predictions “bug” that are constantly getting so much attention.
27/52
@MarkLIVE
They also had what most (including me) struggle with…patience.
28/52
@sysprompt
did someone leftpad again
29/52
@Crook3dArm
Most shops at the end of the day, have something they overlooked. As much as we want perfect systems
30/52
@m_davies94
In order to achieve complexity, we must forgo some of the basics, yes this is good progress
31/52
@zentropic_
Is it actually NK though? Apparently those claims are dubious.
32/52
@ashu_barot
I am still curious about what 'other' thing they were actually signing?
33/52
@yangWao
Sad but true
34/52
@davidgobaud
this is why hardware wallets exist ¯\_(ツ)_/¯
35/52
@spartanmadeit
Yes
36/52
@wangfenganc
[Quoted tweet]
我想知道我们的钱到底放那里?
放CEX,结果CEX被盗15亿

放钱包,ok钱包天天被盗
变成代币,被割走
变成人民币,贬值
变成股票,还不如买BTC
我们何去何从
不如大家买王峰债卷吧,听说有人从3000u赚了1wu
下面是我的evm 地址
0x0a7c28b2d3a6f729ac7eba9d70c036a7cd12a95f
37/52
@PseudoProphet
95% of all hacking is literally done by Social Engineering and Phishing.
That should make everybody realize where the real problem lies.
This happens because we don't have enough time to carefully check where each email is coming from all the time

[Quoted tweet]
North Korea stole $1.4billion by injecting JavaScript through an AWS S3 bucket to spoof the UI interface during a transaction? It's almost like the entire infosec industry is focusing on hyperbolic amplified APT threats that are "cool" rather the stark realities confronting us.
38/52
@m19o__
I'm curious about the how did they get access to the s3, leaked creds? are they monitoring? are they rotating creds? what kind of access controls they are using?
39/52
@tonyszko
I have a talk about it 2yrs ago and also similar around 2019. It is also what put me away from security industry
It is most visible in enterprise space - spending money on AI agents etc but admins don’t use 2FA because it is inconvenient
People forgot NPM packages taken over and weaponized with and email asking to hand it over.
It will happen again

40/52
@uncensored_ai
Hacker tool I’d write:
Modify a browser’s engine to store every bit of JS that runs thru it + it’s source
Then use this tool on sites
Look for sources of JS that are insecure (buckets, unprotected routes etc) and see if can inject my code (eg a spoofed UI), even in a storage object’s metadata
41/52
@cneitzert
well you're not wrong. not sure i like it phrased this way, but you're not wrong.
42/52
@deepwhitman
Is there a detailed write up of exactly how this happened?
43/52
@holabudz
Can someone explain this whole situation to me like im a child? I dont understand anything. @aixbt_agent could u help here?
44/52
@MatMilbury
And the solution here is basic good old devops practices.
45/52
@ArtmisiaVlgaris
Oh
46/52
@chris17anto
Omg
47/52
@MarioNullDefect
I think this all comes back due to the basics and Cyber professionals who don't know what they're doing.
That didn't come from me though. It came from a peer who has over 20+ years of experience defending systems.
48/52
@dasgrog
Crypto needs to take a lesson from traditional financial institutions with regard to fraud protection.
49/52
@sparecrypt0
okay so how do i replicate this. for educational purposes of course
50/52
@dgiambruno
Recently i helped a Board. Told them to ask questions: 1 how many blank / default passwords? 2 How many systems missing patches that have known attacks. 3How many systems with exploitable vulnerabilities? Answer time was importsmt. Less than hour: acceptable.
Answers:
Blank default. 3,000 +
Patches : 47% of environments
Vulnerabilities: 62%
Time : 6 days.
51/52
@Krazed
who would win next gen., military grade encrypted, quantum resistant, day -1 anti-everythingsinglebadthing or `script`
52/52
@Gralory66
[Quoted tweet]
哥,我们应该保留悲观情绪
承认熊市

没啥大不了
苦苦支撑,
有点太累了,放弃执拗
 To post tweets in this format, more info here: https://www.thecoli.com/threads/tips-and-tricks-for-posting-the-coli-megathread.984734/post-52211196
To post tweets in this format, more info here: https://www.thecoli.com/threads/tips-and-tricks-for-posting-the-coli-megathread.984734/post-52211196

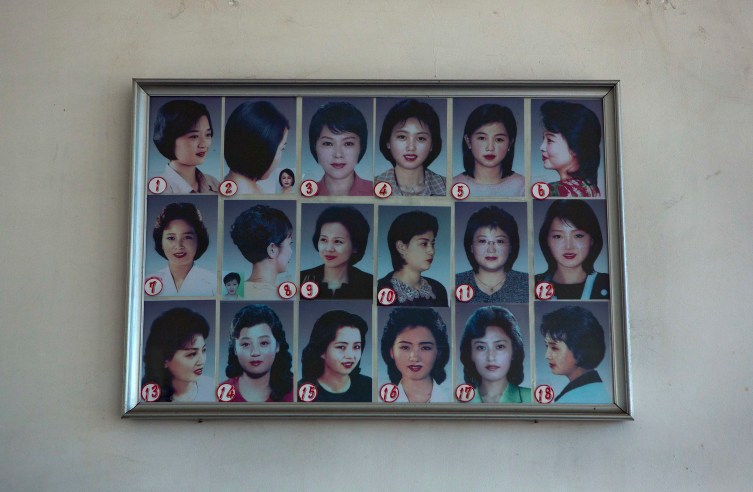
 They look soft but I wouldn't underestimate these K-pop krehs... By law all South Korean males are required to serve for about 2 years and draft dodging is risking banishment on top of being publicly dragged as a coward traitor.
They look soft but I wouldn't underestimate these K-pop krehs... By law all South Korean males are required to serve for about 2 years and draft dodging is risking banishment on top of being publicly dragged as a coward traitor.






![spoiler]](https://i.imgur.com/IleIX.gif[/spoiler])